Today, we’re excited to announce that Platform9 is open-sourcing Klusterkit, a set of three open source tools, available under the Apache v2.0 license on GitHub.
Our customers deploy their software on their private data centers, that are often air-gapped environments (either for security reasons, or other considerations). These large organizations were looking to take advantage of Kubernetes and modernize their applications, while enabling deploying these on different data centers, that are often not connected to the outside world. In comes Klusterkit- to simplify deployment and operations of K8s clusters on air-gapped environments.
Klusterkit is composed of three independent tools, that can be used separately, or in tandem to orchestrate the lifecycle of a production-grade Kubernetes cluster:
- etcdadm, a CLI that simplifies operating an etcd cluster
- nodeadm, a CLI node administration tool that complements kubeadm by deploying the dependencies that kubeadm requires
- cctl, a cluster lifecycle management tool that adopts the Kubernetes community’s Cluster API and uses nodeadm and etcdadm to easily deploy and maintain highly-available Kubernetes clusters in on-premises, even air-gapped environments.
The combination of these three tools enables:
- Easy deployment and operating of highly-available etcd cluster and Kubernetes control plane in air-gapped, on-premise environments using the Cluster API.
- Recovering from a failure of the cluster control plane using etcd backup
- Ability to package all the artifacts required to deploy Kubernetes in an air-gapped environment.
Klusterkit Features
- Multi-master (K8s HA) support
- Deploy and manage secure etcd clusters
- Works in air-gapped environments
- Rolling upgrade and rollback capability
- Flannel (vxlan) CNI backend with plans to support other CNI backends
- Backup and recovery of etcd clusters from quorum loss
- Control plane protection from low memory/low cpu conditions
Klusterkit Solution Architecture
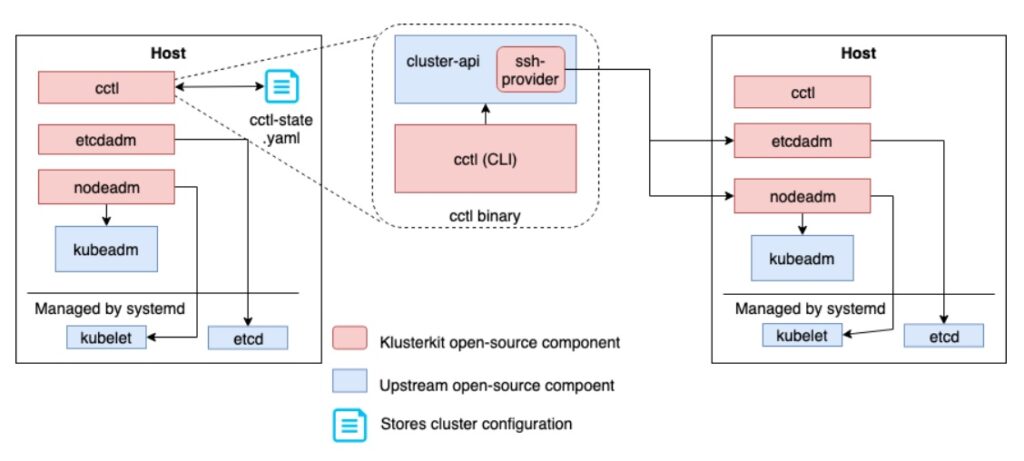
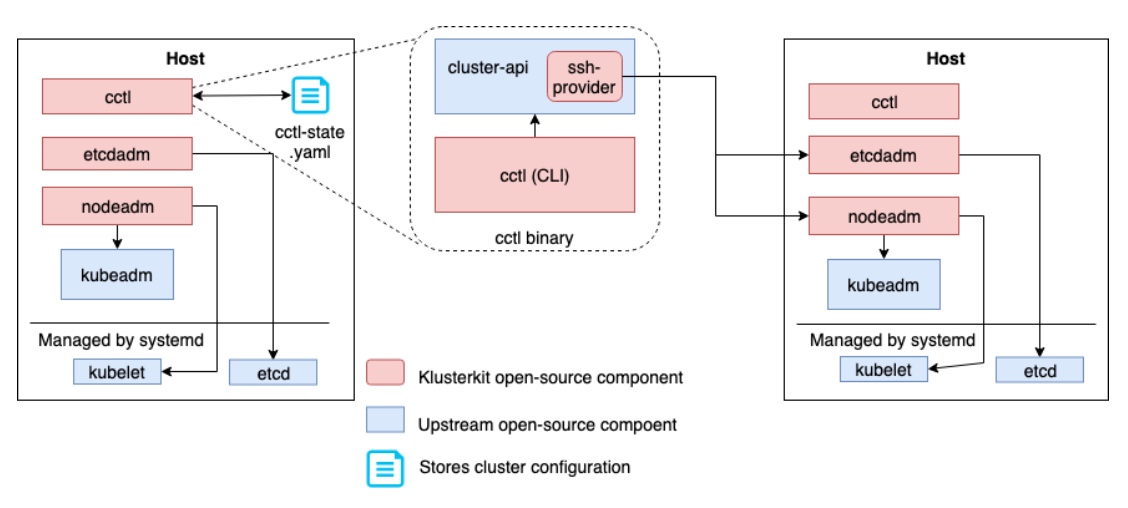
For resiliency and simplicity, Klusterkit uses a single file cctl-state.yaml to store metadata of the Kubernetes cluster you build. The cctl CLI can be invoked to orchestrate the lifecycle of a Kubernetes cluster from any machine which contains this state file. The machine could be an operator’s laptop or any of the machines that are part of the Kubernetes cluster.
Cctl implements and calls into the upstream community cluster-api interface as a library for CRUD operations on clusters. It uses “ssh-provider”, the open-source bare-metal cluster-api provider authored by Platform9, which in-turn calls etcdadm and nodeadm to perform cluster operations.
How to use Klusterkit and its components:
- Each of the three tools can be easily built by calling “go get” as shown below:
go get -u github.com/platform9/cctl go get -u github.com/platform9/nodeadm go get -u github.com/kubernetes-sigs/etcdadm
- These binaries can then be packaged and copied over to the target machines that need to run a highly available Kubernetes cluster. Place the nodeadm and etcdadm binaries in the versioned directories:
cp $GOPATH/bin/nodeadm /var/cache/ssh-provider/nodeadm/<version>/ cp $GOPATH/bin/etcdadm /var/cache/ssh-provider/etcdadm/<version>/
- If the intention is to orchestrate a Kubernetes cluster on-prem, in an air-gapped environment, nodeadm and etcdadm download command makes is easy to pull down required dependencies beforehand from a machine with internet connectivity.These downloaded bits (i.e. kubelet and kubelet systemd file, kubeadm binary, CNI binaries, all container images including Kubernetes, keepalived image and systemd file, etcd container image and related configuration files), can then be copied over to the air-gapped hosts along with cctl, nodeadm, and etcdadm. (For more information see wiki).
- Once all these pieces are in-place, bringing up your first Kubernetes cluster is a couple of commands away:
- First, create the credentials used for the cluster.
$GOPATH/bin/cctl create credential --user root --private-key ~/.ssh/id_rsa
- Then, create a cluster object. Use –help to see a list of supported flags.
$GOPATH/bin/cctl create cluster --pod-network 192.168.0.0/16 --service-network 192.169.0.0/24
- Finally, create the first machine in your cluster.
$GOPATH/bin/cctl create machine --ip $MACHINE_IP --role master
- First, create the credentials used for the cluster.
For more documentation, see GitHub.
Additional information:
- See the technical introduction to nodeadm
- Learn more about etcdadm
- Watch the replay of the CNCF-hosted webinar for a deep-dive into etcdadm – one of the tools included in Klusterkit.